The 4 most popular questions about trigger emails

If you are a marketer, you most probably have already played around with trigger emails: your client is browsing your website, taking a particular action or showing a specific behavioural pattern, and there you go, your trigger email is already on its way.
What are trigger-based emails?
Trigger-based emails are emails sent based on the user’s actions or interactions on the website. If an online shop analyses in real-time the behaviour of its customers and stores this information in a single source, it will know all the opportunities to succeed in selling a product. Then, you can design a personalised sales funnel that will allow you to increase the KPIs.
We have recently interviewed some clients who are already successfully using trigger emails and compiled a short list of questions that quite often concern marketers and
e-commerce specialists. Still not sure about how to get the most out of trigger emails? Here are some frequently asked questions and our best tips.
1. What is better: create trigger chains manually or use ready-made scripts?
Creating trigger maps manually is a long and laborious process. You need to consider how triggers will be combined with each other, decide on the frequency of your emails, connect the customer based on user actions on the website or in the mobile application, and much more. Then empirically check how the chains work, make changes (because the first triggers rarely bring the desired effect) – and so on in a circle.
To reduce time and start getting results faster, we recommend using ready-made solutions. For example, Retail Rocket has a preconfigured trigger communications map with over 40 scenarios. You can see how it looks at the link. We have tested it on millions of users and continuously improved it over the last 7 years.
It will take a couple of days for the system to adapt to your tasks, and right after you will immediately start to see how it benefits your business. A ready-to-use map will also help to eliminate the human factor, aka “oops, we made a mistake”: someone accidentally removed one scenario and screwed the whole system , or a new marketer did not understand the settings of the previous one.
At the same time, you are not limited to a set of 40 behavioural triggers – we also have custom triggers in the form of service and recurring emails. You can come up with the settings for the scripts yourself, and we will take care of the implementation and layout!
2. How to connect customer databases with the website’s behavioural data?
We recognize the user on the site by using their cookies. The process of associating an email address with a cookie goes like this:
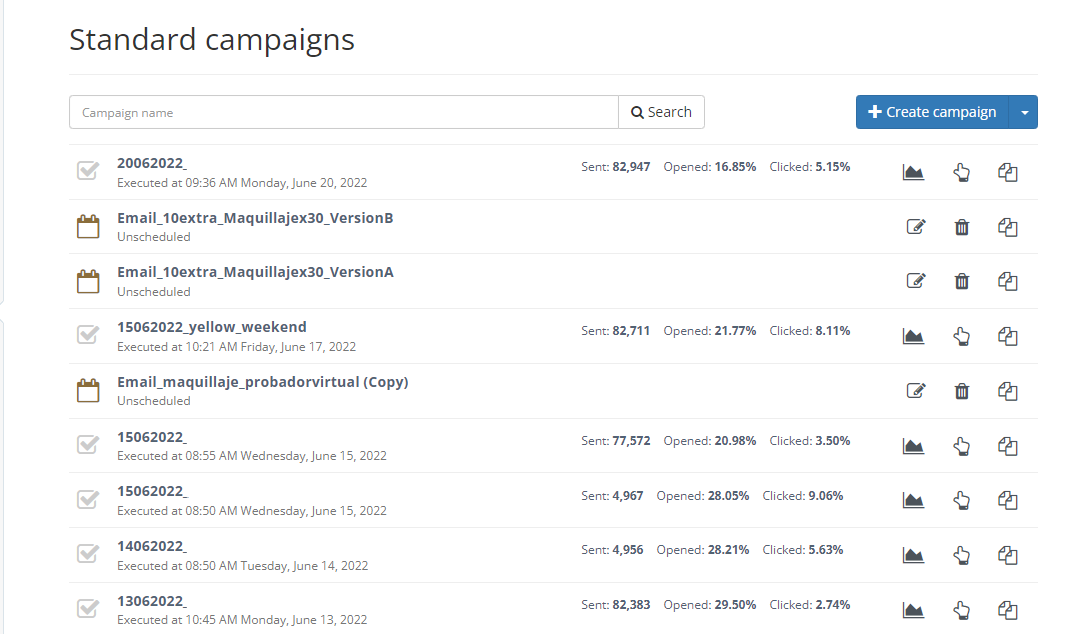
- We have a database of contacts, we add them to the account and carry out a mandatory validation process – this process is key because it allows us to delete invalid contacts;
- After that, we send a mass mailing to the cleaned database (for example, with bestseller items), motivating users to go to visit the website. As a result of this transition, the visitor’s email address is associated with their cookie.
As you might know, from time to time, users delete cookies. In order not to lose those subscribers, once in a while we send automated mass mailings to them and verify cookies.
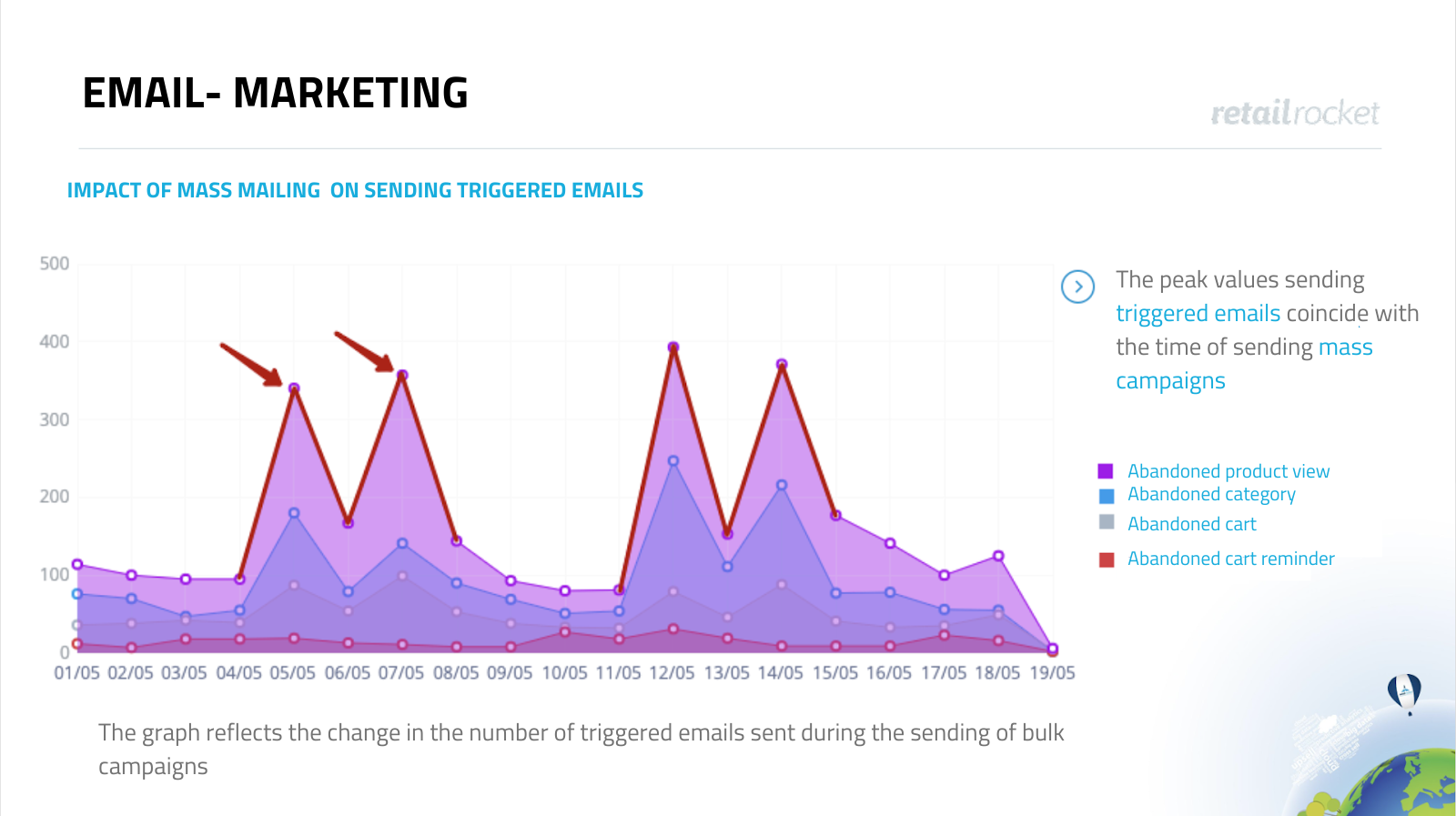
In the screenshot below, you can see that mass mailings directly affect the sending of triggered emails. Therefore, we add the sending of mass mailings for free, as a bonus when a partner is buying a trigger system.
3. Can I set up trigger emails to specific segments?
Yes, you can. In addition to segmentation by behaviour on the website, the audience can be segmented by location, loyalty level, interests, and you can plan automated communication based on these parameters.
As part of our service, we help to think over and set up such custom scenarios. They will be relevant, for example, for retailers with stores in different regions, where prices and availability of goods differ.
An example of how you can use the Customer Intelligence tool to segment users into new, loyal and “at risk”, and set up communication with them. The system checks the conditions – purchases, clicks and other metrics – and based on them sends a relevant email.
4. How not to spam a user?
If the trigger communications map is built manually, you need to carefully consider how the scenarios will be combined with each other, as well as set the optimal time for sending. For example: a user visits the website and adds a refrigerator to the shopping cart. Then he left the site without placing an order, went to the mobile application and started looking at the vacuum cleaners offer. What trigger should be sent to them in this case? Abandoned Cart is a stronger signal, while Abandoned Product View is a newer one.
In Retail Rocket, such dilemmas are excluded, since our algorithm is based on Artificial Intelligence. It collects all information about user behaviour into a database (CDP) and, based on it, decides which trigger, with which products and when to send to that specific client. If more than one trigger matches, the system will automatically select and send the one that is most likely to lead to a conversion.
There is also an additional protection against overspam – the Inactivity hours tool. Thanks to it, you can configure yourself for how long emails should not be delivered. By default, this is 48 hours, that means that a maximum of three emails per week will be sent to the user.
If you want to enable trigger mailings, please book your demo here.
















